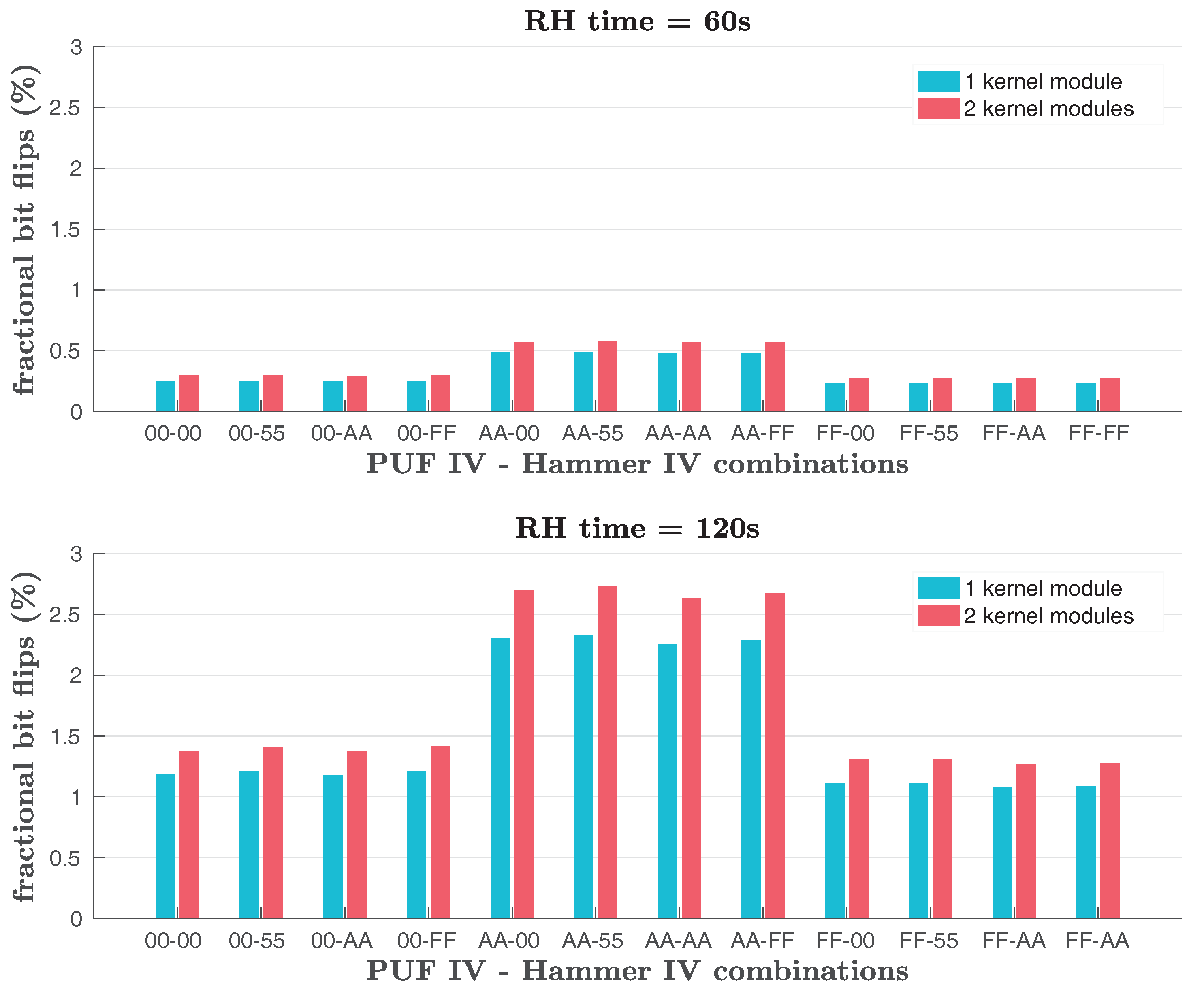
Cryptography | Free Full-Text | Intrinsic Run-Time Row Hammer PUFs: Leveraging the Row Hammer Effect for Run-Time Cryptography and Improved Security †
Cryptography | Free Full-Text | Intrinsic Run-Time Row Hammer PUFs: Leveraging the Row Hammer Effect for Run-Time Cryptography and Improved Security †





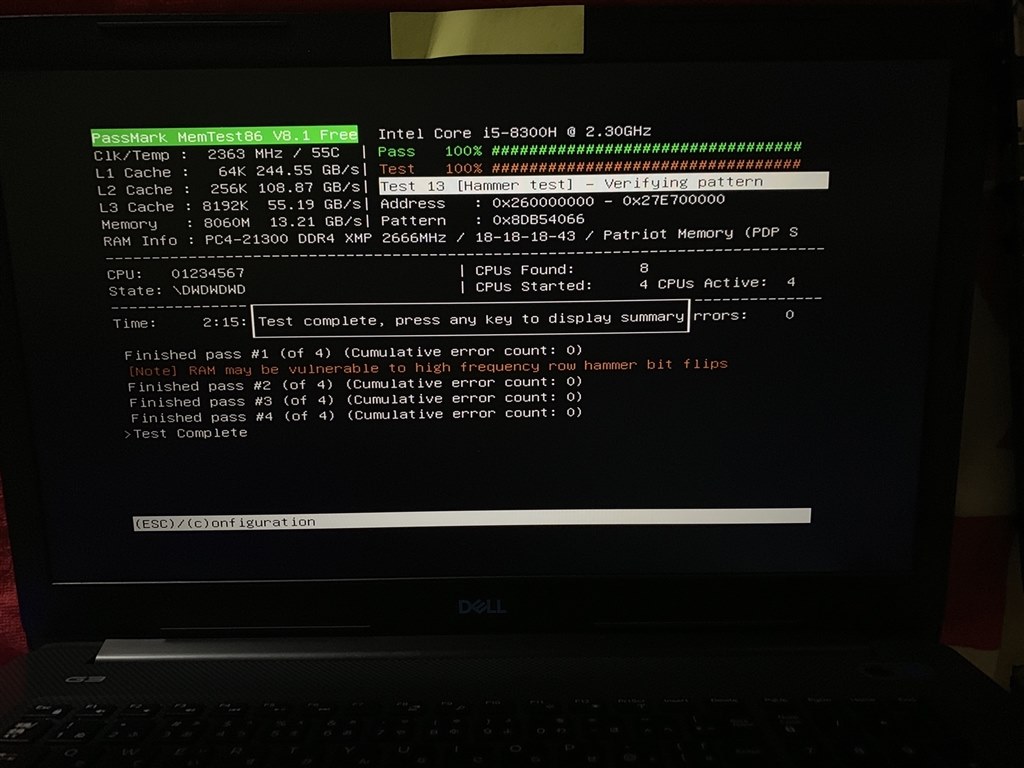
![SOLVED] - How to realiably test the ram stick? | Tom's Hardware Forum SOLVED] - How to realiably test the ram stick? | Tom's Hardware Forum](https://i.imgur.com/3JZFd3i.jpg)